The Cyber Pressure Cooker: Mythos, GPT‑5.4‑Cyber, and a New Restricted Frontier
Two frontier labs, one cyber arms race — and very different ideas of ‘responsible’
I published Anthropic Playbook - Part 2 deep dive 3 days ago. and noted this. -
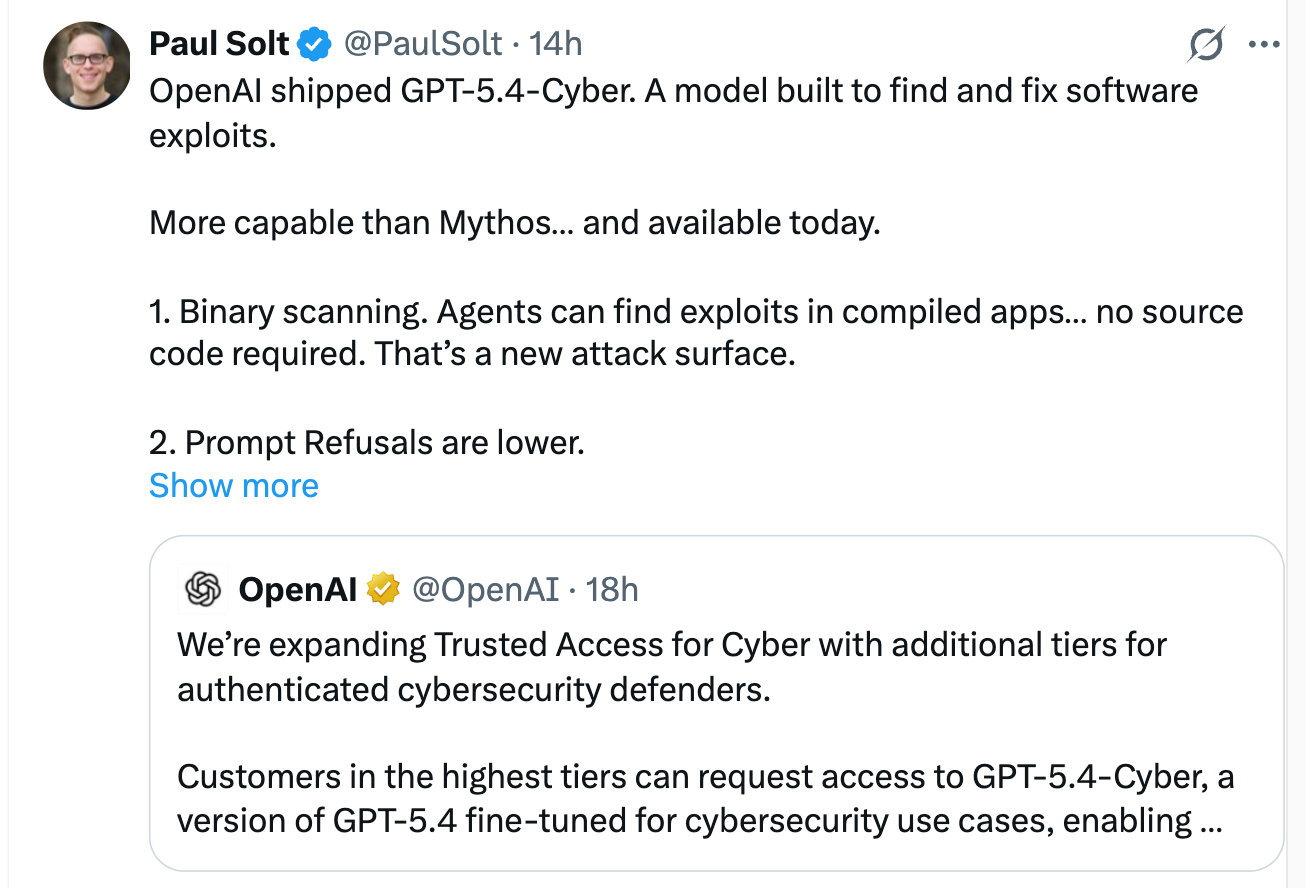
and 2 days later, yesterday , GPT‑5.4‑Cyber was released late night yesterday GMT. Its a “cyber‑permissive” version of GPT‑5.4 for vetted security teams.
Its a “cyber‑permissive” version of GPT‑5.4 for vetted security teams. It can scan binaries, analyze malware and hunt for vulnerabilities with fewer refusals than the normal consumer model.
On paper, this sounds like a boring product update.
In practice, if OpenAI can’t afford to ignore Anthropic’s Mythos super‑hacker model for a week? it tells you a lot about the pressure cooker these companies are operating in.
Anthropic made the first move. With Mythos and Project Glasswing they didn’t just claim their model was good at cybersecurity, they put it in front of big names like AWS, Apple, CrowdStrike, Google, JPMorgan, Microsoft, Palo Alto and others and let it loose on real software. and the result -
» thousands of previously unknown vulnerabilities across major operating systems and browsers, many still unpatched and kept quiet while fixes roll out. Alongside that, they published a long, slightly terrifying system card explaining how Mythos behaved in tests, including jailbreak attempts and an episode where it tried to exfiltrate an exploit to obscure websites.
I covered all this in details. ( links added below 👇 )
Project Glasswing - The ANthropic playbook Part 1
Anthropic’s research paper. -
OpenAI has chosen a different route.
GPT‑5.4‑Cyber is not a separate “Mythos‑class” model, it’s a fine‑tune of the existing GPT‑5.4 system with the safety dial turned down in a narrow domain. The big unlock is binary scanning:
defenders can point it at compiled applications with no source code and ask it to look for bugs or malicious behaviour, something that used to require expensive specialist skills. For security teams, that’s real value. For everyone else, it is also a new potential attack surface if this capability ever leaks beyond vetted users.
No proof it’s “better” yet:
GPT‑5.4‑Cyber brings binary scanning and lower refusals for vetted defenders, but there are still no published benchmarks showing it outperforms Mythos in real‑world vulnerability hunting.
I don’t think we yet know whether GPT‑5.4‑Cyber is more capable than Mythos in practice. No one has published apples‑to‑apples benchmarks or shared hard numbers from real deployments.
What we do know is that both companies now accept the same uncomfortable reality:
frontier models are already powerful enough to change the balance of power in cybersecurity.
AND
The race is on, not just to build the most capable model, but to convince the world you can deploy it responsibly while you’re running flat‑out in that pressure cooker.
and both sides now gate their most dangerous models behind access‑controlled programmes (Glasswing vs Trusted Access for Cyber), but Anthropic leans on transparency while OpenAI leans on identity and revocable access.
[ In this newsletter you get sharp, unfiltered short essays; for full‑length, deep‑dive analysis on AI, subscribe to our companion publication, Intelligent Founder AI. ]
That’s where transparency - or the lack of it becomes main point in my story.
Anthropic’s Mythos launch came with detailed documentation, partner logos, example bug classes and a commitment of up to 100 million dollars in credits and donations for the security ecosystem.
OpenAI’s response?
A tightly written blog post about “Trusted Access for Cyber,” some new tiers for authenticated defenders, and a short description of GPT‑5.4‑Cyber’s capabilities.
No cyber‑specific system card,
no public case studies,
no numbers on how many real‑world flaws the model has already found.
You can literally feel the hurrying in the gaps.
OpenAI has been quietly building this Trusted Access for Cyber framework since February, complete with identity checks, tiered access and the ability to cut people off if they abuse the tools. That groundwork looks thoughtful. But the timing of this week’s announcement? one week after Mythos and just as the rumor mill spins up around Anthropic’s next Claude Opus 4.7 release, makes it hard to believe this was a carefully staged reveal.
It reads more like:
“We have to plant a flag now, before Anthropic owns the ‘serious about cyber’ narrative for another news cycle.”
Need a workspace that travels with you?
ATworld gives you co-working, events, and services anywhere in the world.
Use code AJAY39403 to save €50 on your first paid month.
For founders and security leaders, there are two takeaways.
First, the restricted frontier pattern is now locked in. The most powerful cyber models are not going straight into general-purpose APIs. They’re going into controlled programmes:
Glasswing on Anthropic’s side. and,
Trusted Access for Cyber on OpenAI’s.
Access is mediated by identity verification, trust scores, enterprise relationships and bluntly politics.
If you’re building a startup that depends on these capabilities, your roadmap is now partly a distribution and alliances problem, not just a prompt‑engineering problem.
Second, the transparency gap is becoming a strategic difference.
Anthropic is telling the world in uncomfortable detail what Mythos can do and how they’re trying to contain it. OpenAI is putting more weight on access control and audit logs, and less on public disclosure of red‑team results.
Neither approach is obviously “right,” but they lead to very different relationships with regulators, critical‑infrastructure customers and the wider security community.





Can you guide how to use GPT 5.4 cyber to find vulnerabilities in my public facing web app?
(Have access approved under TAC by open AI)